Discover the essence of network forensics, an investigative process that uncovers digital evidence and identifies cyber threats….
In this comprehensive article, we delve into the world of penetration testing types, uncovering the various types…
In this article, we will guide you through the process of installing Docker on Kali Linux, a…
Welcome to the Ultimate Kerberos Penetration Testing Guide! In this step-by-step tutorial, we will dive deep into…
Secure Shell (SSH) is a fundamental protocol for secure remote access, enabling users to connect to remote…
Infrastructure Penetration Testing is a critical aspect of any organization’s security strategy. In this article, we will…
Today I am writing about CVE-2020-1472 (ZeroLogon) and how can be detected with CrackMapExec and then exploit…
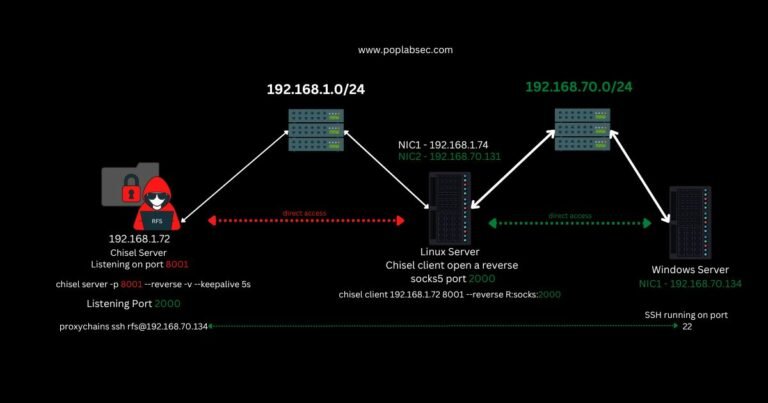
Welcome, today I will talk about Pivoting with Chisel Reverse Proxy, in this tutorial we will get…
How to Install Bloodhound on Linux and correct Java problems. Install JAVA and Dependencies Bloodhound requires several…
Methodology To Attack a Linux Machine Ok after scanning the network we detect some Linux machines and…